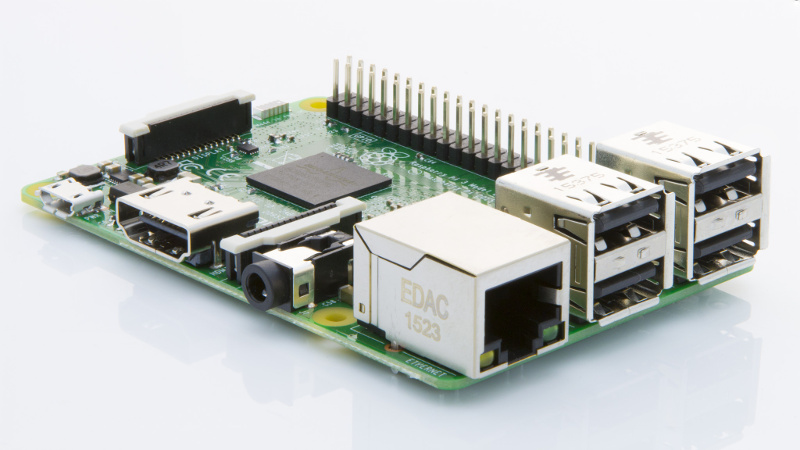
A Linux malware, Linux.MulDrop.14, that infects Raspberry Pi devices has been detected. The malware was spotted around the mid of May 2017 with the aim of mining cryptocurrency on Raspberry Pi devices with Rasberry Pi 2 being the most vulnerable.
According to Dr. Web, the Russian antivirus maker, the malware comes in the form of a Bash script which contains a mining program that is compressed with gzip and is encrypted with base64. After it is launched, the script shuts down many processes and installs libraries such as Zmap and sshpass required for its operation.
The malware targets Raspberry Pi devices that are using default login and password with SSH ports open to external connections. It gains access to the device by using the default Raspberry Pi login “pi” and password “raspberry”.
The malware changes the user’s password and goes on installing the cryptocurrency mining programs. Afterward, it installs Zmap, the Internet-scanning tool, to scan the Internet for other vulnerable Raspberry Pi devices with open SSH port and default login credentials.
To protect your device from this malware, you have to:
- Update the operating system. By doing this, the SSH port id is disabled.
- Change the default password. The best way to stop the malware attack is by changing your default password and login since they infect by using the Raspberry Pi default user and password.
